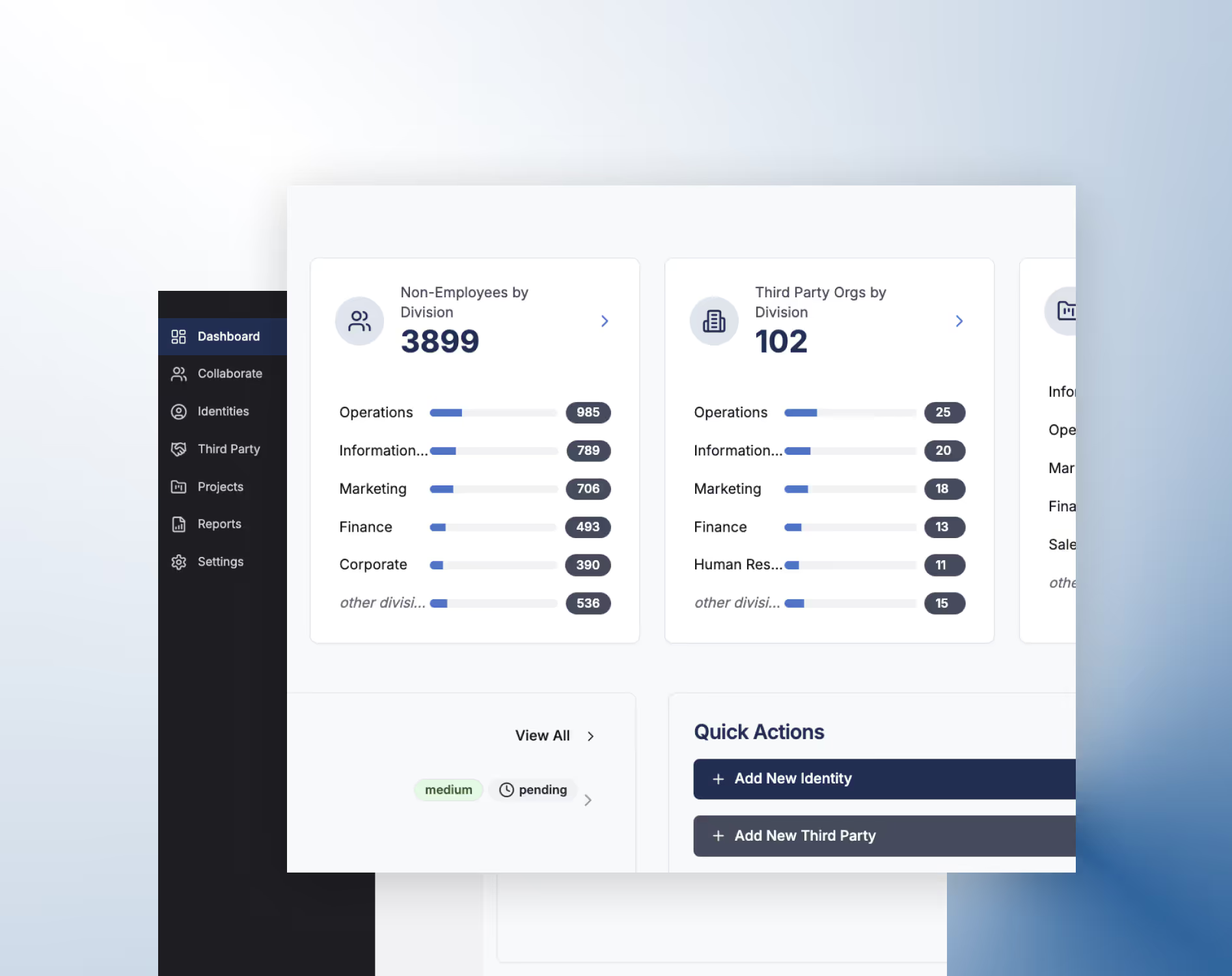
The identity platform for third-party and non-employee governance
idGenius gives teams control over the fastest-growing identity risk: external access. Automate lifecycle management, enforce governance, and scale secure vendor identities—without the overhead.

Trusted by teams securing complex environments






























Built for the identities your HR system doesn’t see
Contractors. Vendors. Partners. Machines. These users power your business—but rarely fit neatly into traditional IAM.
idGenius is purpose-built to govern external identities from first access to final offboarding.

Delegate identity ownership with full auditability—internally or externally

Enforce policy with automated approvals and expirations

Onboard external users fast—no code, no confusion

Maintain visibility across every external identity, role, and access trail
Third-party identity is
your biggest blind spot
Unmanaged third-party access can lead to orphaned accounts, audit failures, and avoidable breaches.
Traditional IAM tools weren’t built for this. But we are.
Smarter software. Stronger security. Less manual work.

AI-powered identity intelligence
Understand who has access, how, and why—in real time.

Secure vendor management
Manage vendor identities, project scopes, and timelines from a single platform.

Delegated management
Delegate identity management internally or externally—without giving up control.

Document management
Centralize background checks, contracts, and compliance docs for each identity and organization.

End-to-end lifecycle automation
Provision, modify, and retire third-party identities without spreadsheets or tickets.

Audit-ready from day one
Track approvals, documents, expirations, and ownership history—automatically.

Built for high-stakes
environments
We are trusted by teams in complex, compliance-heavy sectors, such as:

Vendor governance and fraud prevention

Secure PHI and affiliated
access

Manage contributor and contractor identities

Align with NIST, FICAM, and Zero Trust mandates
See idGenius in action
Watch how idGenius simplifies onboarding, manages third-party identities, and automates identity governance—all in a single, purpose-built platform.
Automate identity governance with idGenius
Manual tasks in third-party identity management can create delays, errors, and compliance gaps. idGenius helps you streamline approvals, notifications, and lifecycle events across systems. No code required. Just smarter, faster governance.
.avif)
Streamline lifecycle management
Automate lifecycle tasks across onboarding, offboarding, and identity updates.
Auto-initiate deprovisioning when contracts end.
Alert sponsors when access is about to expire.
Keep downstream systems synced with current identity status.
Enforce consistency with
ease
This integration helps enforce consistency and scale your identity governance.
Reduces manual effort and eliminates process gaps.
Speeds up onboarding and response times.
Enables scalable, policy-driven governance across the business.
Simplify your workflows
Delegate and route approvals without compromising oversight or compliance.
Automate multi-step approvals based on project or region.
Escalate overdue tasks without manual follow-up.
Push status updates to audit and reporting tools.
We’re not just solving identity. We’re solving the part everyone else missed.
Anomalix is a software development company focused on one mission: building the smartest platform for third-party identity governance.