IAM advisory services
Align your identity strategy with business goals and risk
Whether you're building a new identity program or optimizing an existing one, our advisory services give you the strategic foundation to move forward with confidence.
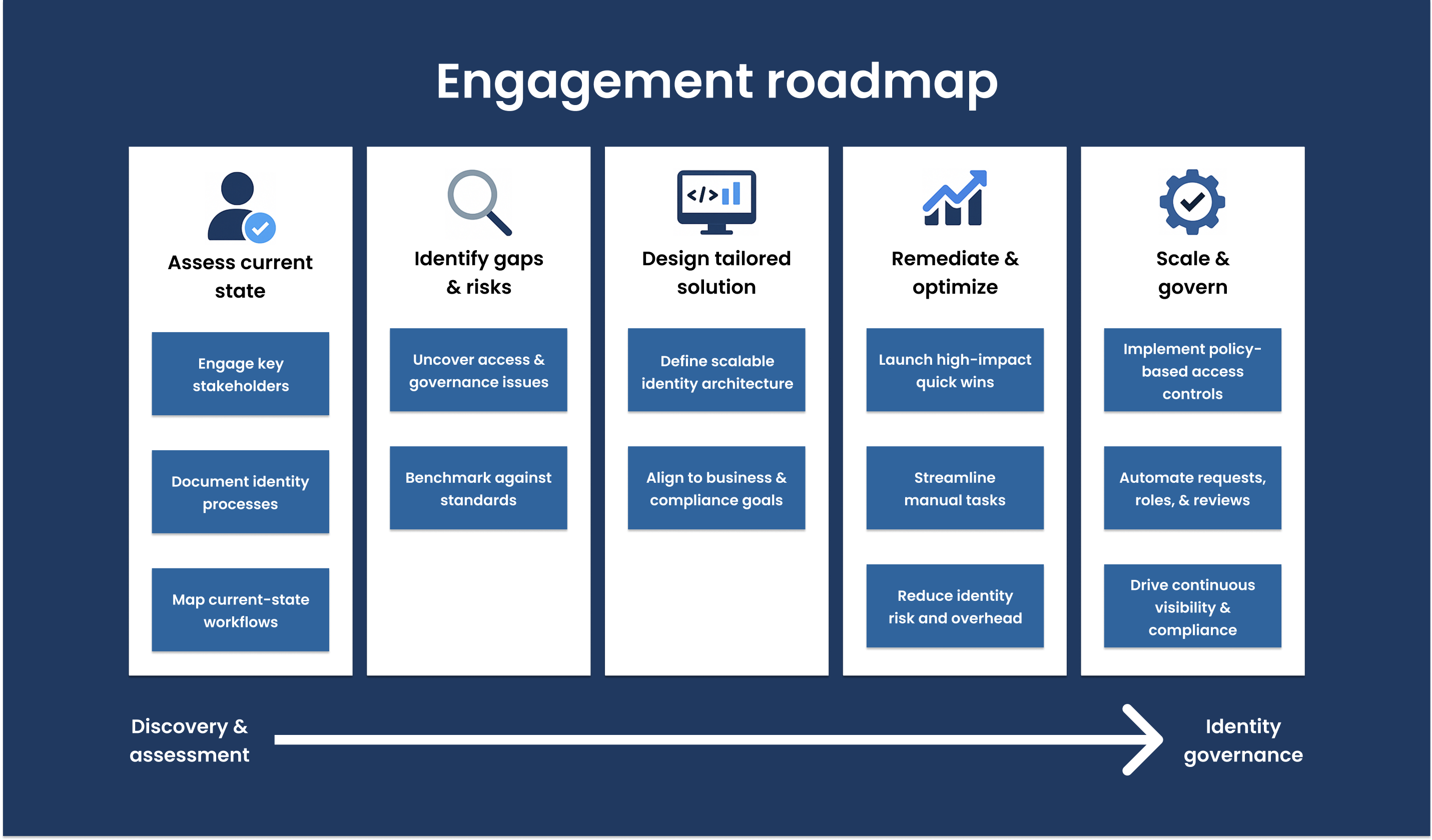
We help you define a clear vision, assess your current state, and build a roadmap that connects identity governance to your broader business objectives.

What we deliver

Identity governance and compliance assessments
Get a detailed analysis of your current IAM environment, identifying gaps, inefficiencies, and compliance risks across employee and non-employee identities.
Strategy and roadmap development
We work with your stakeholders to define measurable goals, maturity models, and phased roadmaps that align IAM efforts with your digital transformation, Zero Trust, and regulatory initiatives.
Security framework alignment
We align your IAM strategy with standards like NIST, ISO 27001, and industry-specific compliance mandates (HIPAA, SOX, PCI DSS, etc.), enabling you to support audits and reduce risk.
Our approach
Our advisory services are designed to be collaborative, actionable, and scalable. We bring cross-functional experience in IT, security, and compliance—and we tailor every engagement to your business needs and organizational maturity.

Stakeholder workshops and interviews

Gap analysis and priority mapping

Technical and process audits

Deliverables you can take straight to leadership
How our clients benefit
A business-aligned IAM roadmap ready for executive review
Defined requirements for IAM architecture and access models
Prioritized list of remediation efforts and quick wins
Recommendations for tools, workflows, and governance processes
Clear strategy for employee, third-party, and privileged identities

Supporting your long-term identity goals
Advisory services are just the beginning. Our consulting, implementation, and managed services teams can help you turn strategy into execution—seamlessly integrating the platforms and processes your roadmap requires.