Third-Party Identity Security in 2026: What CISOs Need to Know
Introduction: Identity Is Still the Attack Surface—But It’s Not Who You Think
By 2026, most CISOs agree on one thing: identity is the new perimeter.
What’s less universally acknowledged is whose identities matter most.
For years, organizations have poured resources into securing employee access—modern IAM, SSO, MFA, PAM, zero trust architectures. Yet the fastest-growing identity population inside most enterprises is no longer employees. It’s third parties: contractors, vendors, consultants, service providers, outsourced teams, system integrators, and increasingly, non-human identities like service accounts, bots, APIs, and AI agents.
This extended workforce now outnumbers employees in many enterprises. They access the same systems, touch the same data, and often operate with higher privileges—yet they remain the least governed identities in the environment.
At Anomalix, we see this disconnect every day. Organizations believe they have strong identity security, but when you look beyond HR-managed users, the reality is far more fragile. Third-party identities live in spreadsheets, ticketing systems, procurement tools, emails, and tribal knowledge. Offboarding depends on memory. Access reviews are manual and incomplete. Ownership is unclear.
As we move deeper into 2026, this is no longer sustainable. Regulatory pressure is rising, attackers are targeting third-party pathways, and business dependence on external identities is accelerating.
Third-party identity security is not a future concern. It is today’s defining identity challenge.

Why Third-Party Identity Risk Is Exploding in 2026
1. The Extended Enterprise Is Now the Default Operating Model
Modern enterprises are ecosystems, not organizations.
Cloud platforms, SaaS tools, outsourced IT, managed security services, offshore development, M&A integrations, and digital supply chains all rely on external access by design. Speed to market demands rapid onboarding of third parties, often across multiple systems and environments.
The problem is that identity governance did not evolve at the same pace.
Traditional IAM assumes:
- A single employer
- HR as the source of truth
- Stable roles
- Predictable lifecycles
Third-party identities break every one of those assumptions.
They belong to external organizations, shift between projects, require temporary or elevated access, and frequently leave without a clean termination signal. This mismatch creates systemic blind spots that attackers—and auditors—are increasingly exploiting.
2. Attackers Are Actively Targeting Third-Party Identities
The data is clear: third-party access is now one of the most reliable breach vectors.
Why?
Because attackers don’t need to defeat your strongest controls if they can walk in through your weakest ones.
Third-party identities often:
- Bypass MFA requirements
- Use shared or generic accounts
- Retain access long after contracts end
- Have broad entitlements “just to get the job done”
- Are rarely monitored with the same rigor as employees
A compromised vendor credential can quietly provide persistent access without triggering alarms. In 2026, threat actors understand this better than many defenders.
3. Compliance and Regulation Are Catching Up to Reality
Frameworks and regulations are evolving to reflect the risk of unmanaged third-party access.
Whether it’s PCI DSS, ISO 27001, SOC 2, NIST CSF, GDPR, or emerging supply-chain regulations, the expectation is clear:
organizations must govern all identities—not just employees.
Auditors now ask:
- Who owns this vendor account?
- Why does it still exist?
- What data can it access?
- When was it last reviewed?
- What happens when the contract ends?
Without dedicated third-party identity governance, these questions are hard—often impossible—to answer confidently .
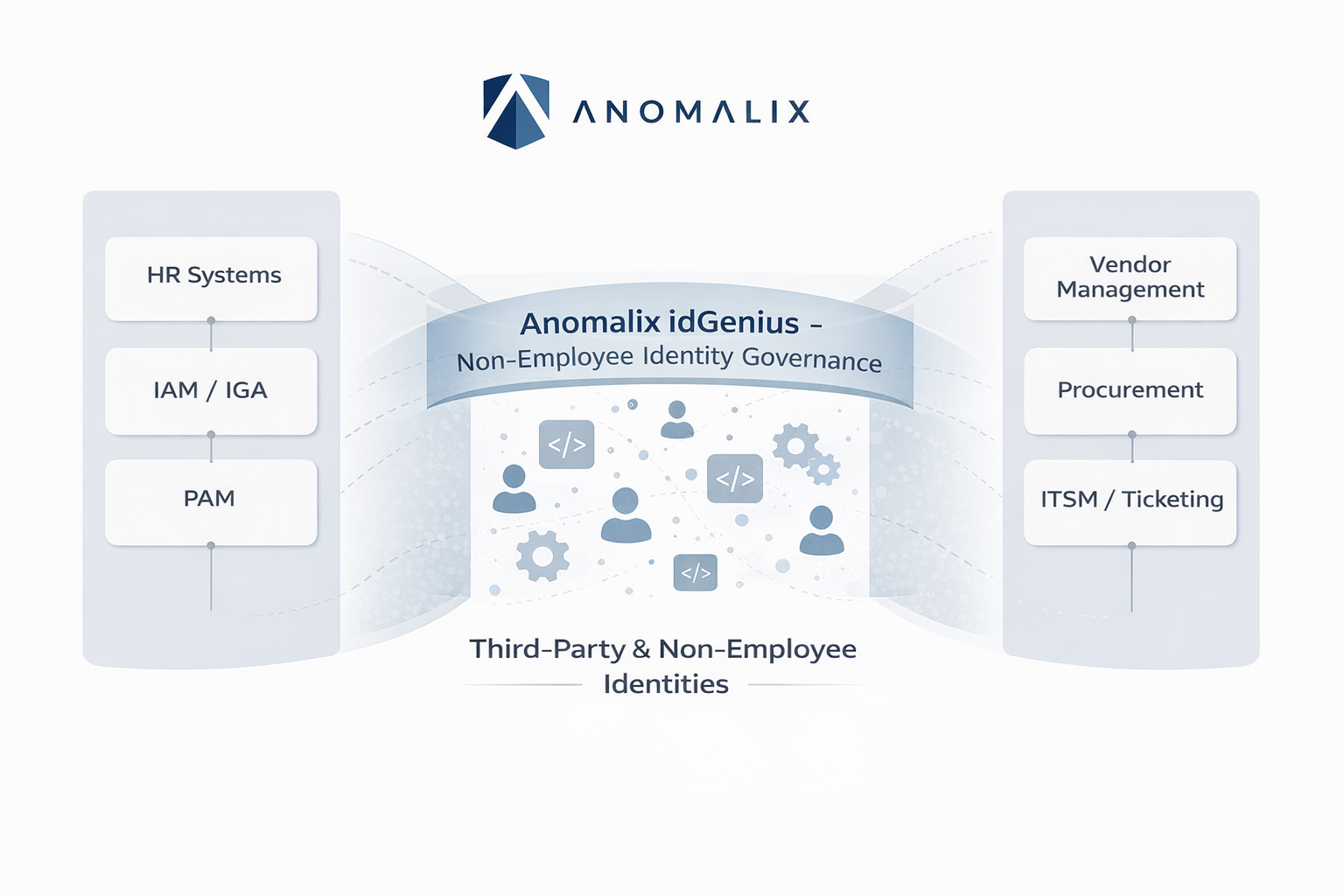
The Core Problem: Third-Party Identities Fall Between Systems
One of the biggest misconceptions CISOs still face is believing that existing tools can simply be “extended” to cover third-party identities.
In practice, third-party identities fall into a governance gap between systems:
- IAM / IGA is employee-centric and HR-driven
- Vendor management tracks contracts, not access
- Procurement knows who was hired, not what they can reach
- ITSM manages tickets, not lifecycles
- Security tools see behavior, not business context
As a result, no system owns the full lifecycle of a third-party identity.
At Anomalix, we describe this as the missing identity layer—a dedicated governance fabric for non-employee and third-party identities that bridges business context, access control, and risk intelligence .
What “Good” Third-Party Identity Security Looks Like in 2026
By 2026, mature organizations are moving beyond ad-hoc fixes and embracing a fundamentally different approach to third-party identity security.
Here’s what CISOs should be aiming for.
1. Third-Party Identity Is a First-Class Identity Category
The most important mindset shift is this:
third-party identities are not exceptions—they are a core identity population.
That means:
- They have structured identity records
- They are tied to real organizations, contracts, and sponsors
- They follow defined join-change-leave processes
- They are governed continuously, not periodically
Treating third-party users as “temporary employees” is a recipe for over-privilege and orphaned access.
2. Business Context Drives Access—Not Tickets
In 2026, access decisions must be driven by context, not convenience.
That context includes:
- Which third-party organization the identity belongs to
- Which contract or engagement authorizes access
- Which project they are assigned to
- What systems and data are required
- How long the access should exist
- Who is accountable internally
Without this context, least privilege is theoretical. With it, least privilege becomes enforceable and auditable .
3. Time-Bound Access Is the Default
Indefinite access is one of the biggest contributors to third-party risk.
In mature environments:
- Every third-party identity has an expiration date
- Access is automatically revoked unless explicitly renewed
- Extensions require justification and approval
- Dormant access is eliminated by design
This single control dramatically reduces attack surface and audit exposure.
4. Ownership and Accountability Are Explicit
Every third-party identity must have a clearly defined internal owner—typically a business sponsor.
That owner is accountable for:
- Requesting access
- Approving scope
- Reviewing access periodically
- Confirming when the engagement ends
When ownership is unclear, risk is inevitable. Governance only works when accountability is explicit.
5. Identity Risk Is Dynamic, Not Static
In 2026, third-party identity security cannot rely on static controls.
Risk changes when:
- A contractor gains privileged access
- A vendor operates from a new geography
- A project expands in scope
- An identity behaves anomalously
- A parent organization experiences a breach
Modern identity governance must continuously reassess risk and adapt access accordingly—tightening controls when risk increases and removing friction when it decreases.
The Anomalix Point of View: Identity-First, Third-Party-First Security
At Anomalix, our perspective is simple and unwavering:
identity is the control plane of cybersecurity, and third-party identities are where that control plane is weakest today.
Most organizations don’t fail at third-party security because they lack policies. They fail because those policies are impossible to operationalize with employee-centric tools.
That’s why we focus exclusively on non-employee and third-party identity governance.
Our approach is built on a few core principles:
One Source of Truth for Third-Party Identity
Organizations need a centralized system that understands:
- Third-party organizations
- Their people and machine identities
- Contracts, projects, and sponsors
- Risk attributes and expiration dates
Without this foundation, everything else is guesswork.
Lifecycle Governance, Not Just Access Provisioning
True security comes from governing the full lifecycle:
- Structured onboarding
- Controlled changes
- Automated offboarding
- Continuous certification
Access provisioning is only one step in a much larger identity story.
Automation Over Manual Effort
Manual reviews, spreadsheets, and ticket queues do not scale—and they don’t stand up to audits.
Automation ensures:
- Consistency
- Speed
- Auditability
- Reduced human error
This is how governance becomes sustainable.
Designed to Complement Existing IAM, Not Replace It
Third-party identity governance is not a rip-and-replace initiative.
It is a missing layer that integrates with existing IAM, PAM, ITDR, and security tooling—adding the context and controls those systems were never designed to handle.
Where idGenius Fits
idGenius is Anomalix’s purpose-built platform for third-party and non-employee identity governance.
It provides:
- Centralized visibility into third-party identities and organizations
- Contract- and project-based access governance
- Time-bound, policy-driven provisioning
- Automated lifecycle management
- Audit-ready reporting
- AI-driven risk and anomaly insights
Most importantly, idGenius aligns identity security with how the business actually operates—across vendors, partners, contractors, and machine identities—without slowing the organization down.
What CISOs Should Be Doing Now
As 2026 unfolds, CISOs should be asking a few hard questions:
- Do we know how many third-party identities exist in our environment?
- Can we confidently explain why each one has access?
- Do those identities automatically lose access when engagement ends?
- Can we prove this to an auditor—today?
- Do we treat third-party identity as a strategic security control, or an operational nuisance?
If the answers are uncomfortable, that’s not a failure—it’s a signal.
The organizations that lead in the next phase of cybersecurity will be the ones that bring third-party identity security out of the shadows and into the center of their strategy.

Conclusion: Third-Party Identity Security Is the Next Identity Frontier
In 2026, identity security is no longer just about employees, passwords, or MFA. It’s about governing the full identity ecosystem that powers modern business.
Third-party identities represent the fastest-growing, least-controlled, and most exploited segment of that ecosystem. Ignoring them is no longer an option.
At Anomalix, we believe that securing the extended workforce requires a purpose-built approach—one that treats third-party identity governance as a foundational security discipline, not an afterthought.
When identity is governed with context, automation, and accountability, security becomes stronger, compliance becomes easier, and the business moves faster with confidence.
Contact us at info@anomalix.com to learn how our idGenius platform can help you govern your extended workforce with confidence, security, and ease.
Mohammed Elkhatib is Founder and CEO at Anomalix. Prior to founding Anomalix, Mohammed led global operations for Aveksa (acquired by RSA) where he was responsible for Sales, PreSales, Engineering and Professional Services. Mohammed is an Identity Security expert with over 25 years of IT and Business experience.