Multi-Factor Authentication
Compromised account credentials continue to be at the heart of cybercrime, leading to data breaches, systems held hostage by ransomware, and installation of malware. These losses continue to increase dramatically year over year, and as the hackers increase the sophistication of their attacks, it becomes more and more difficult to defend. According to Microsoft, implementing a Multi-Factor Authentication (MFA) solution can block 99.9% of account hacks. Yet, a study conducted by LastPass shows that only 57% of companies have implemented an MFA standard. Implementation of an MFA process is crucial to securing account credentials and should be prioritized for implementation into enterprise IT environments.
The default authentication is usually Single Factor, where access is granted through one category of credentials, most often with the use of a Username and Password. Multi-factor authentication adds an additional layer of security by requiring two or more pieces of information to be presented to an authentication mechanism. These are some common MFA schema medias often utilized:
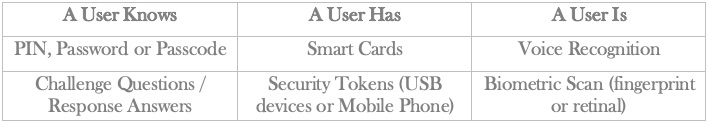
MFA can be set up for both employees (internal and external to the company firewall) or customers (external to the company firewall) to provide a secure form of authentication. Most default security systems involve setting up something the User Knows (passwords, security questions, etc.). Once the initial credentials have been submitted correctly, the system will recognize the User and challenge them with additional requests based on something previously setup. The second layer could be something the User Has (text or call to a phone number, encrypted code from a third-party application or a physical external token), or it could be something that the User Is (biometric attribute – fingerprint, facial recognition, retinal scan).
Implementation of MFA is extremely flexible, utilizing easy to obtain data points such as:
- Hardware Tokens
- Soft Tokens
- Phone Call
- Time-based One-Time Password (TOTP)
- Short Message Service (SMS) / Text Message
- Electronic Mail (Email)
- Push Notifications
- Security Questions (Hashed Questions with Encrypted Answers)
MFA implementations must support and integrate into existing business applications, systems, networks, and processes without affecting the current workflows in order for it to be effective. The different types of MFA solutions allow the IT departments plenty of flexibility as they balance the user experience with security. MFA can be implemented to handle several different types of use cases with alternative factors such as time-based one-time passwords, short message service (text message), electronic mail (email), or push notifications. Some of these factors may be more ideal per application than others based on the situation. For example, mail can be encrypted and sent over secure tunnels, whereas text SMS is not a secure means of electronic authentication. But for a new employee without email access looking to set up their email for the first time, the one-time SMS text would provide additional security and solve the problem of not having email access. Another standard solution that can alleviate pain points is the incorporation of the MFA solution in which a help desk or support website can provide a secure yet seamless solution when the end-user has exhausted their options. For instance, an end-user has forgotten an account password and locked their account. Correctly, answering a pre-defined set of security questions will unlock the account.
It is essential for a company to construct an expandable yet seamless MFA security map, whether that is cloud-based, locally hosted, or set in off-site locations. The objective of combining two or more authentication protocols together is to help reduce the risk of being compromised.
MFA can reduce the account hacks from situations such as brute force attacks, stolen hardware, and compromised passwords. The schemes provide additional layers of security over the simple username/password model. The IT industry continues to improve future expansions of MFA offerings such as geolocation tags and expanding biometric attributes to help pave the way for a seamless MFA experience. This also helps pave the way for self-service solutions, reducing the need and cost of a large HELP desk operation.
Multi-factor authentication is necessary for a company to succeed in today’s market, but a much more expandable MFA model to include adaptable authentication is recommended. No matter how large or complex an enterprise is, MFA is an easy and cost-efficient security solution to protect the enterprise yet provide scalability in the future.