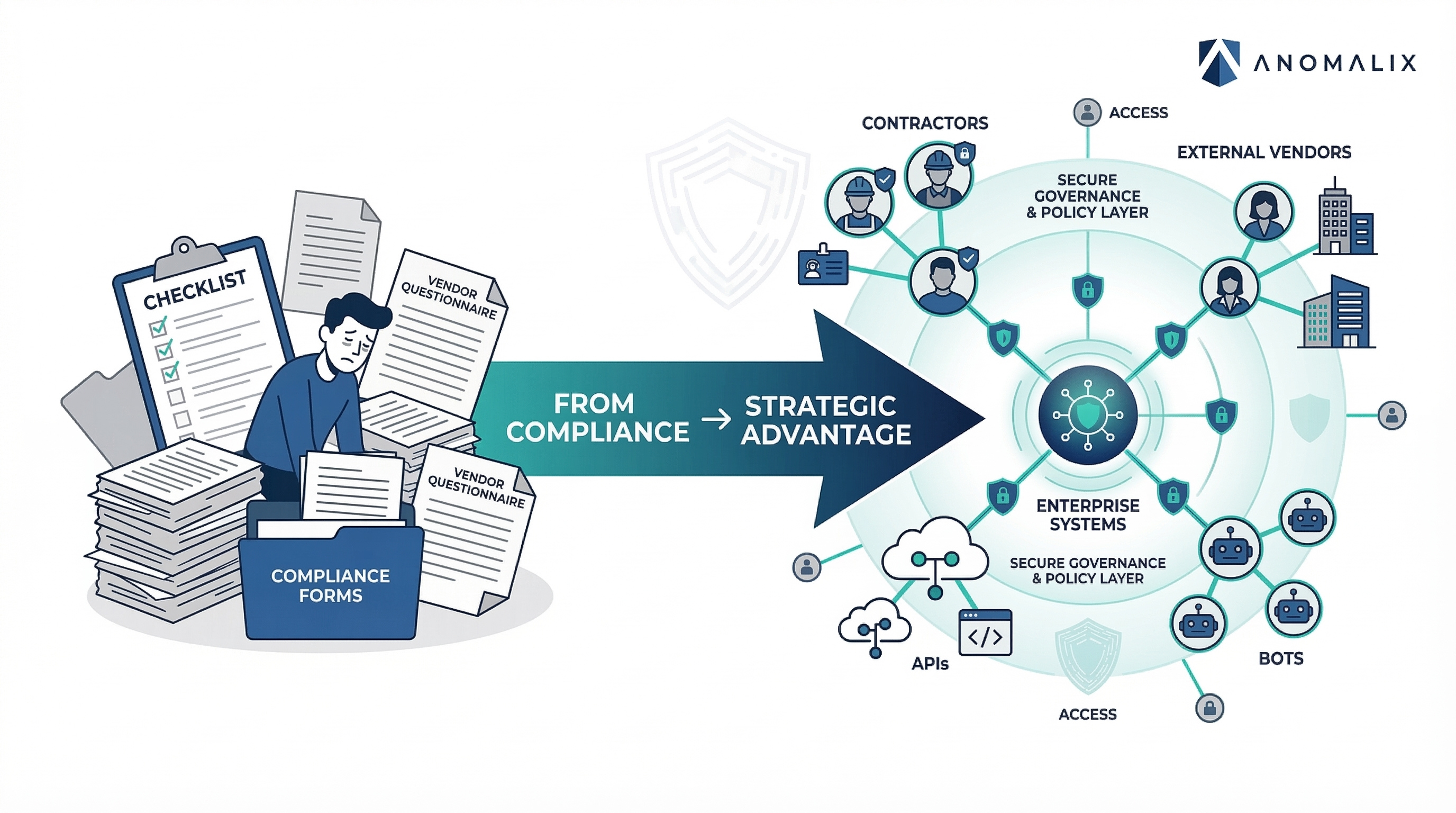
From Compliance to Strategic Advantage: Rethinking Third-Party Risk Management
Introduction: The Evolution of Third-Party Risk
Modern enterprises rarely operate within the boundaries of a single organization anymore. Today’s businesses depend on a vast ecosystem of vendors, contractors, suppliers, service providers, consultants, and partners. These external entities enable innovation, accelerate delivery, and provide specialized expertise—but they also introduce one of the most complex risk surfaces organizations must manage.
Third-party risk management (TPRM) was originally designed as a compliance-driven function. Organizations assessed vendors through questionnaires, contractual obligations, and periodic audits to ensure they met regulatory expectations. While these controls remain important, they are no longer sufficient for the realities of the modern digital enterprise.
The reason is simple: risk now flows through identities and access, not just through contractual relationships. Vendors, contractors, and external service providers frequently access sensitive systems, data, and infrastructure. Yet many organizations still govern these relationships primarily through documentation rather than operational control.
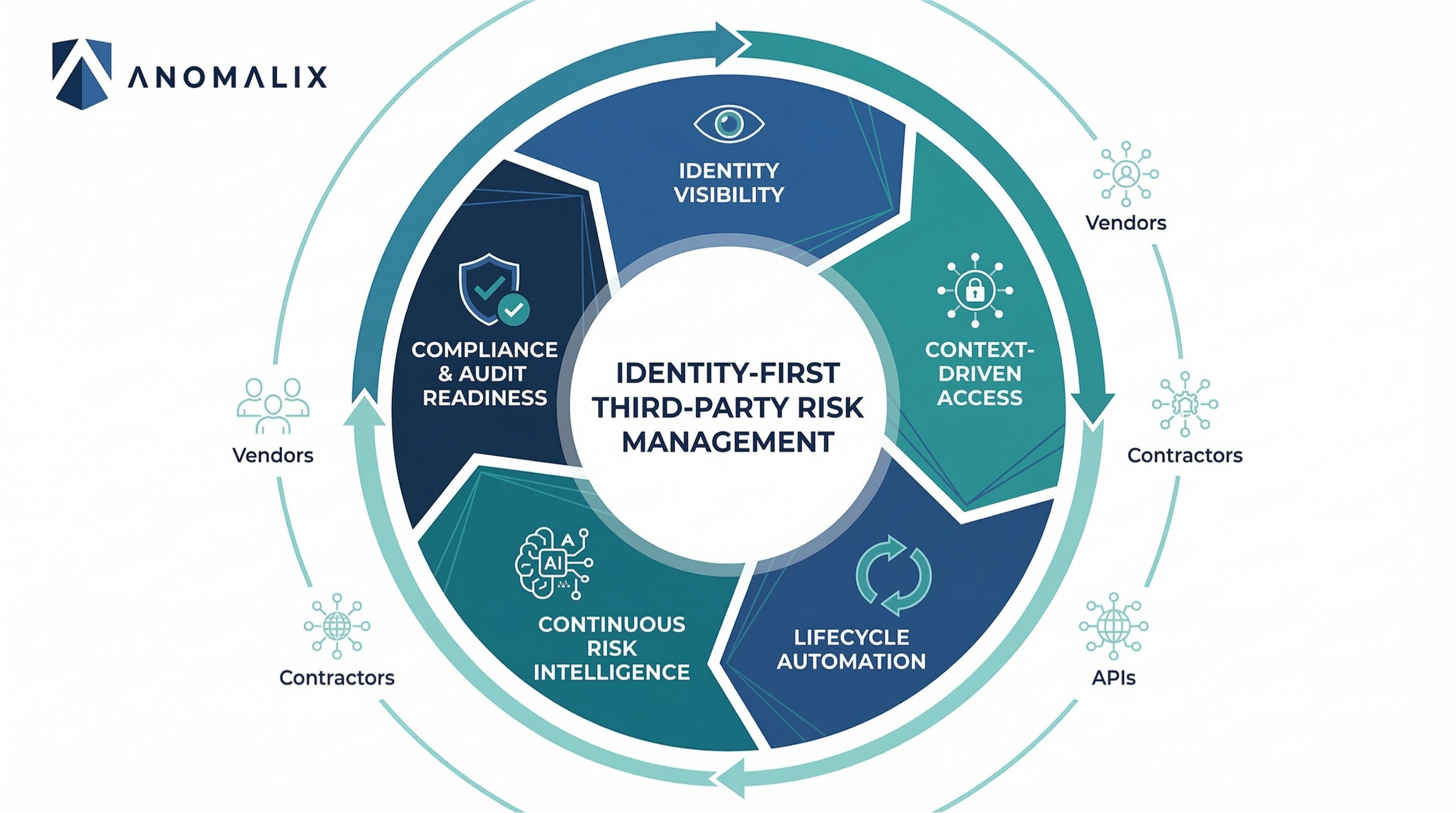
At Anomalix, we believe the next evolution of TPRM lies in shifting from compliance-driven oversight to identity-driven governance. When organizations rethink third-party risk management as a strategic identity security capability, they unlock not only stronger protection but also improved business agility and trust across the extended workforce.
Why Traditional Third-Party Risk Management Is No Longer Enough
Historically, third-party risk management focused on evaluating vendors before engagement. Security teams would review certifications, examine policies, and verify compliance with frameworks such as SOC 2, ISO 27001, or PCI DSS.
While these practices remain necessary, they have a fundamental limitation: they evaluate the organization, not the identities interacting with your systems.
The traditional TPRM model typically includes:
- Vendor security questionnaires
- Contractual security clauses
- Periodic vendor risk assessments
- Annual or quarterly compliance reviews
- External security ratings
These processes provide valuable insight into the security posture of the vendor organization, but they rarely control what individual vendor identities can actually access inside your environment.
This gap creates several critical issues:
1. Access Decisions Happen Outside the Risk Program
While procurement and risk teams evaluate vendors, the operational reality is that access decisions are often made by business units, IT teams, or application owners. These decisions frequently occur through ad hoc processes such as tickets, email requests, or direct account creation.
As a result, access governance becomes fragmented, inconsistent, and difficult to audit.
2. Risk Is Static While Access Is Dynamic
Traditional TPRM assigns vendors a risk rating that rarely changes until the next assessment cycle. Meanwhile, vendor employees, contractors, and machine identities gain and lose access continuously as projects evolve.
Without real-time identity governance, risk quickly drifts away from the original assessment.
3. Compliance Doesn’t Equal Security
Organizations may technically pass vendor assessments and still experience breaches through third-party identities.
A vendor can have strong security controls internally while their accounts inside your systems remain:
- Over-privileged
- Poorly monitored
- Untracked after contract termination
This disconnect between compliance and operational access control is where many modern security incidents originate.
The Extended Enterprise: Where Third-Party Risk Lives Today
Modern enterprises operate as interconnected ecosystems rather than isolated organizations.
Cloud platforms, SaaS applications, managed service providers, offshore development teams, system integrators, and API-based integrations all require external access to internal systems.
This creates what many security leaders call the extended enterprise—a network of identities operating across organizational boundaries.
In many large organizations, the number of non-employee identities now equals or exceeds the number of employees. These include:
- Contractors
- Consultants
- Vendor personnel
- Managed service providers
- Partner organizations
- Temporary workers
- Machine identities such as APIs, bots, and service accounts
These identities often access the same systems and data as internal employees, yet they frequently lack the same governance controls.
From a risk perspective, this imbalance creates a dangerous blind spot.
Third-party identities tend to:
- Exist outside HR systems
- Follow inconsistent onboarding processes
- Have unclear ownership or sponsorship
- Accumulate privileges over time
- Persist long after the engagement ends
Without proper governance, these identities quietly expand the organization’s attack surface.
The Real Problem: Third-Party Identities Fall Between Systems
One of the biggest structural challenges in modern cybersecurity is that third-party identities do not clearly belong to any existing control system.
Different departments manage different aspects of vendor relationships:
Function
Focus
Procurement
Contracts and vendor selection
Vendor Management
Relationship governance
IAM
Employee identity management
Security Operations
Monitoring and threat detection
IT
Account provisioning
None of these systems fully govern the lifecycle of third-party identities.
Traditional identity and access management tools rely heavily on HR systems as the source of truth, which works well for employees but fails for external identities that originate from contracts, projects, or vendor relationships.
This creates a governance gap where:
- Vendor contracts exist without linked identity controls
- Identity accounts exist without lifecycle ownership
- Security tools see activity but lack business context
Closing this gap requires a fundamentally different approach to third-party risk management.
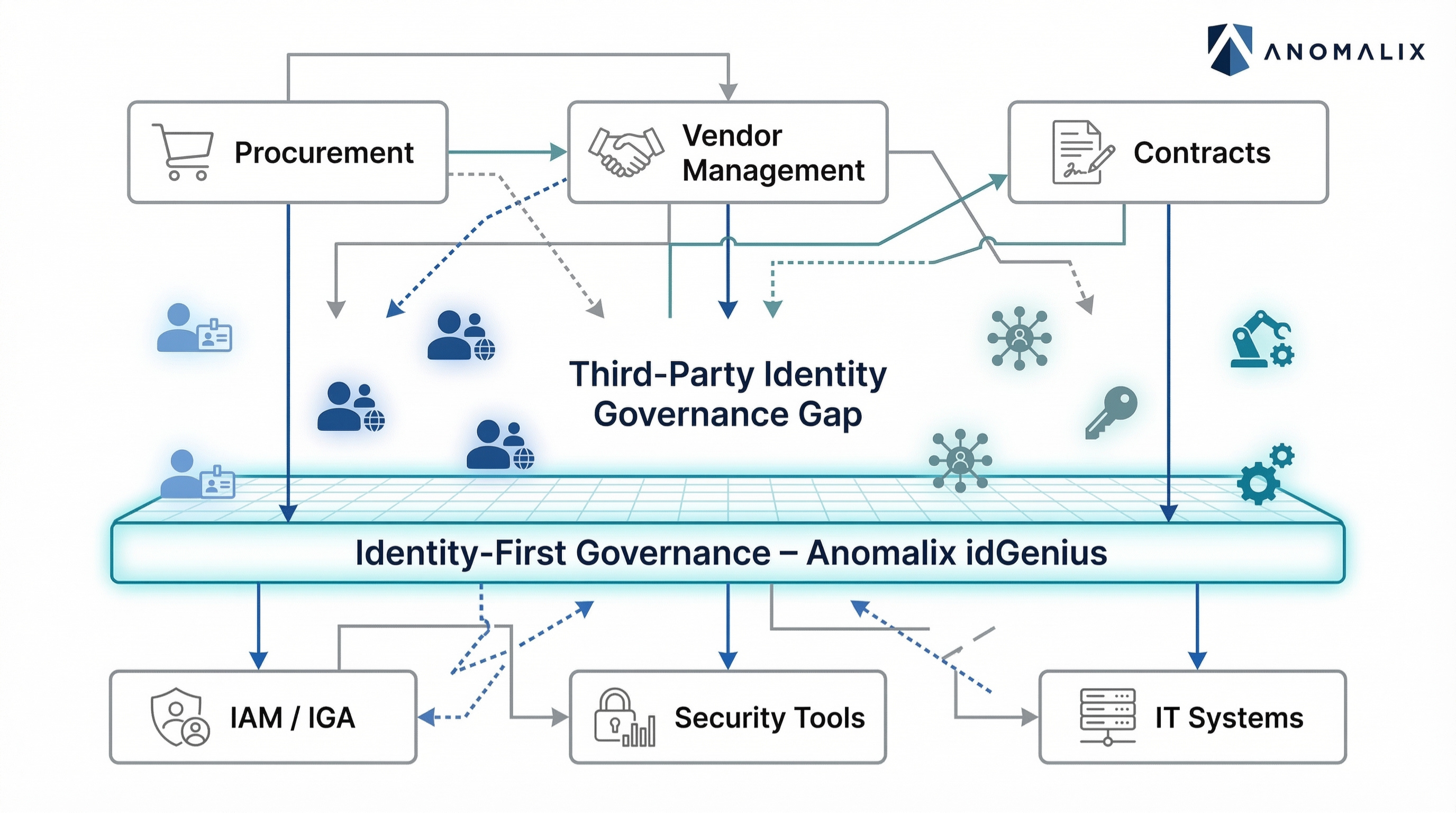
Identity-First Third-Party Risk Management
At Anomalix, we believe the future of TPRM is identity-first.
Identity-first third-party risk management shifts the focus from evaluating vendor organizations to governing the identities that interact with your environment.
Instead of asking:
“Is this vendor trustworthy?”
Identity-first TPRM asks:
- Which identities from this vendor have access?
- What systems and data can they reach?
- Why do they need that access?
- Who is accountable for it?
- When should it expire?
This shift transforms TPRM from a periodic assessment process into a continuous operational security capability.
Identity-first vendor governance ensures that every external identity is:
- Known
- Accountable
- Contextualized
- Time-bound
- Continuously monitored
This approach connects risk management directly to access governance, closing the gap between policy and operational security.
From Compliance Exercise to Strategic Capability
Organizations that rethink TPRM through an identity-first lens begin to see a significant transformation. Third-party risk management evolves from a reactive compliance task into a strategic business enabler.
1. Real-Time Visibility into the Extended Workforce
Identity-centric governance creates a centralized inventory of all external identities and their access.
Security teams gain visibility into:
- Third-party organizations
- Individual users and machine identities
- Access privileges and entitlements
- Project assignments and contract timelines
- Sponsoring business units
This level of transparency allows organizations to understand their true attack surface.
Without this visibility, security teams cannot answer even basic questions about external access.
2. Access Aligned with Business Context
Traditional access provisioning often happens without understanding the broader business relationship behind the request.
Identity-first TPRM ties access decisions directly to:
- Vendor contracts
- Project assignments
- Sponsoring departments
- Risk ratings
This ensures that external identities receive only the access required to perform their tasks, reinforcing least privilege principles.
Over time, this dramatically reduces the number of excessive permissions and dormant accounts in the environment.
3. Lifecycle Governance Instead of One-Time Reviews
External identities often move between roles, projects, and organizations. Their access needs change frequently.
An identity-first approach governs the entire lifecycle of these identities:
- Structured onboarding
- Policy-driven access provisioning
- Automated access adjustments
- Time-bound entitlements
- Automated offboarding
When access is tied directly to engagement timelines, dormant accounts disappear by design rather than by manual cleanup.
4. Continuous Risk Intelligence
In traditional TPRM programs, risk assessments occur periodically.
Identity-first governance enables continuous risk monitoring by linking identity activity to security analytics.
Risk signals may include:
- Unusual access behavior
- Dormant accounts
- Privileged entitlements
- Access from unexpected geographies
- Vendor breach notifications
This dynamic risk model allows organizations to adjust controls in real time rather than waiting for the next assessment cycle.
Business Benefits of Strategic Third-Party Risk Management
When third-party risk management evolves beyond compliance, organizations experience tangible business advantages.
Faster Vendor Onboarding
Manual vendor onboarding processes often delay projects.
Automated identity workflows enable organizations to onboard external users quickly while maintaining security controls.
This improves collaboration without increasing risk.
Reduced Security Incidents
Identity governance significantly reduces common breach vectors such as:
- Orphaned vendor accounts
- Over-privileged contractor access
- Shared or unmanaged service accounts
By governing these identities continuously, organizations shrink their attack surface.
Stronger Compliance and Audit Readiness
Regulators increasingly expect organizations to demonstrate control over third-party access.
Frameworks such as:
- PCI DSS
- ISO 27001
- SOC 2
- GDPR
- NIST CSF
all emphasize strong identity governance and least-privilege enforcement.
Identity-first TPRM provides audit-ready visibility into:
- Who has access
- Why they have it
- Who approved it
- When it will expire
This dramatically simplifies audit preparation and reduces compliance risk.
Stronger Vendor Trust and Collaboration
When organizations implement structured identity governance, vendor relationships become more transparent and predictable.
Vendors benefit from:
- Faster access provisioning
- Clear onboarding requirements
- Defined responsibilities
- Consistent processes
This improves operational efficiency across the digital supply chain.
The Anomalix Point of View
At Anomalix, we believe the future of cybersecurity is identity-driven—and third-party identities are the most overlooked part of that equation.
Modern enterprises rely on external ecosystems to operate, yet most identity security strategies remain focused almost entirely on employees.
This mismatch creates systemic blind spots where risk accumulates.
Our perspective is clear:
Identity is the control plane of modern cybersecurity, and third-party identities must be governed with the same rigor as internal users.
Through the idGenius platform, Anomalix helps organizations operationalize identity-first third-party risk management by providing:
- Centralized visibility into third-party organizations and identities
- Contract- and project-based access governance
- Automated lifecycle management
- Time-bound access enforcement
- AI-driven risk intelligence and anomaly detection
By aligning identity governance with vendor lifecycle management, idGenius enables organizations to move beyond reactive compliance and toward proactive security.
Conclusion: Turning Third-Party Risk into Strategic Advantage
Third-party risk management is at a turning point.
The traditional model—focused on vendor questionnaires and periodic assessments—was built for a different era. In today’s digital ecosystem, risk flows through identities and access paths, not just through vendor relationships.
Organizations that continue to treat TPRM as a compliance function will struggle to keep pace with the complexity of the extended enterprise.
But organizations that rethink TPRM as an identity governance discipline unlock something far more powerful: a strategic advantage.
With identity-first third-party risk management, organizations gain:
- Visibility into their extended workforce
- Real-time control over external access
- Continuous risk intelligence
- Faster collaboration with partners and vendors
- Stronger security and compliance outcomes
Most importantly, they move from reacting to third-party risk to actively governing it.
The future of third-party risk management isn’t just about assessing vendors—it’s about governing the identities that connect your business to the world.
Contact us at info@anomalix.com to learn how our idGenius platform can help you govern your extended workforce with confidence, security, and ease.
Mohammed Elkhatib is Founder and CEO at Anomalix. Prior to founding Anomalix, Mohammed led global operations for Aveksa (acquired by RSA) where he was responsible for Sales, PreSales, Engineering and Professional Services. Mohammed is an Identity Security expert with over 25 years of IT and Business experience.